IN LATE February the stolen personal information of 10.6 million MGM Resorts guests was posted to a hacking forum forcing the hotel chain to admit there had been a data theft the previous summer.
It was the latest in a series of high-profile cybercrimes involving some of the biggest names in finance, insurance, entertainment, and hospitality, although in this case, the company said it was “confident” no financial information had been exposed and the data was confined to “phonebook” information.
Between 2013 and 2019, Yahoo, Facebook, First American, Equifax, Adult Friend Finder, Capital One, and Marriott, all suffered data breaches involving more than three billion people.
Marriott revealed in 2018 that someone had had unauthorised access to its guest reservations system for nearly five years and said the personal details of approximately 500 million guests could have been exposed, including passport numbers and credit card details.
The hospitality data thefts serve as a warning to the wider business meetings industry. Overall, cybercrime will cost victims more than US$6 trillion annually by 2021, according to global research company Cybersecurity Ventures.
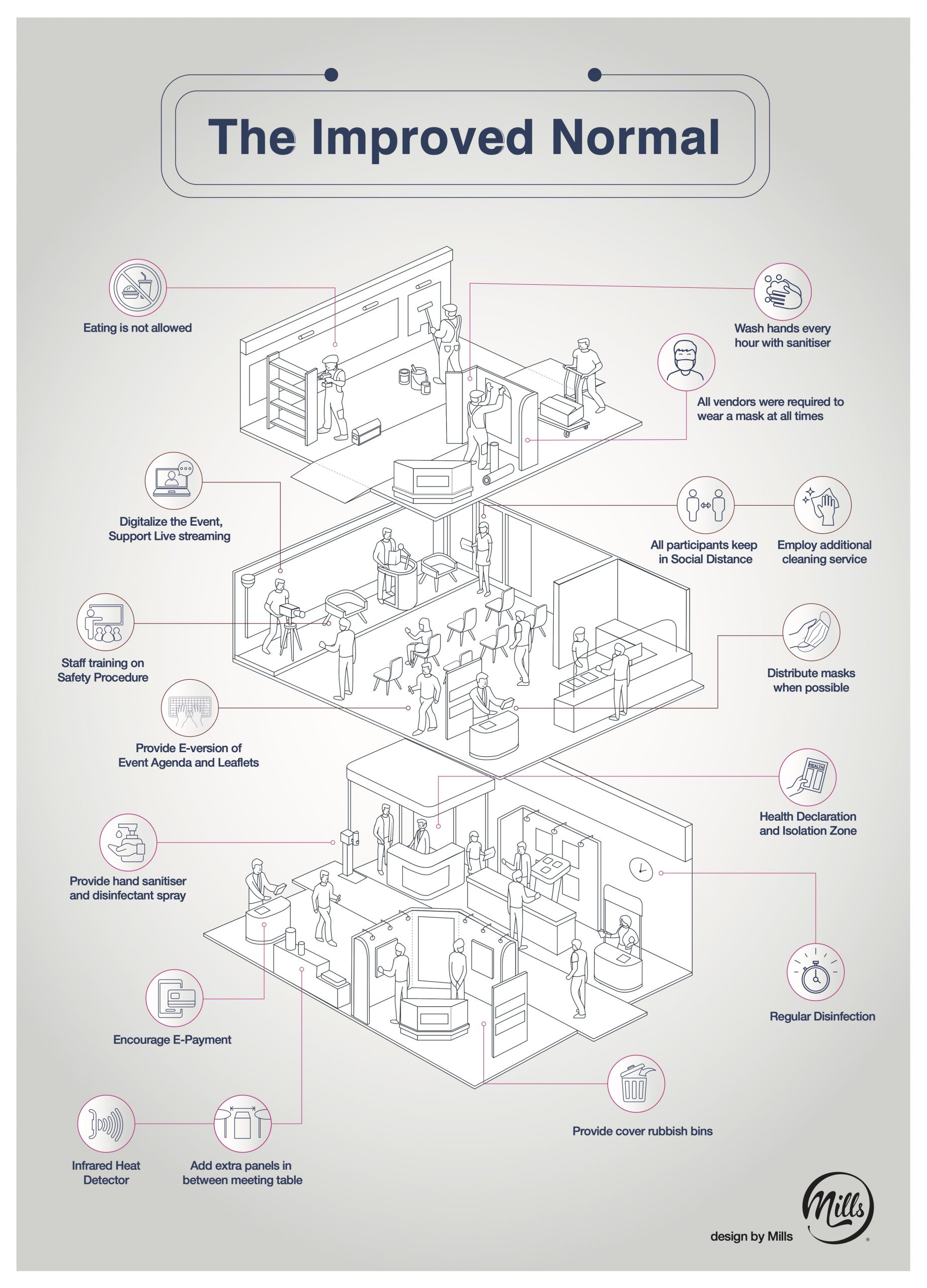
As the benefits of event apps, high-speed 5G-assisted web tech, and AI automation increase, so too, do the risks, with planners, organisers and meetings hosts increasingly becoming the guardians of huge amounts of business and personal information.
Hong Kong-based Central Pacific Consultants, working with tech partner Zkipster, recently published a guide advising planners how to avoid the pitfalls.
First, they say, it is important to have an event-tech security strategy plan, starting by mapping out all the “touch points” – possible items at risk that need to be addressed. These might include the event main database, emails, seating tools, and check-in apps.
Action items should then be defined to protect each point using digital security best practices. Tips include:
- Consolidated and vetted tools – do research and pick trusted and well-vetted partners for all technology needs.
- Individual accounts and audit logs – when there is more than one person working with guest data in event software, it is vital to know who’s doing what.
- Use multi-factor log-in authentication.
- Adopt automated password policies – many professional-grade tools now offer the ability to enforce users to create safer passwords.
- Ensure correctly provisioned access levels – err on the side of giving team members or partners the minimum level of access needed to do their work.
- Eliminate human error – where possible, automate processes in the workflow that can be susceptible to people making mistakes.
- Provide training to prevent phishing and other forms of manipulation.
- Carry out regular digital housekeeping.
- Have a clear plan of action for when things do go wrong.
Despite high-profile cases of data theft, there is a lack of urgency among events planners when it comes to taking preventative action, says Sean Donahoo, CEO of cybersecurity specialists Disruptive Solutions.
“The meetings industry is not taking this seriously at all,” Donahoo says. “It kills me. I see how things are done, and all of the planning that goes into events. Everything is planned for down to a T, except this part, and it’s maybe the most important part, if you look at it from a reputation standpoint.”
Travel industry intelligence provider Skift quotes John Sileo, CEO of the Sileo Group, which offers cybersecurity training, as saying that low-profile data breaches are commonplace.
“I probably get a call a month or more from a planner who has had a meeting breached, or one of their attendees was breached, which happens as much, if not more, and that’s where the huge liabilities come up,” he says.
Sileo and Donahoo say there are many reasons to hack a meeting.
“Often this is about corporate espionage or corporate ransom,” Sileo says. “Let’s say there’s a conference for the federation of employee benefit plans. Managers of the plans have social security numbers, credit card numbers, and retirement account information on employees for 5,000 of the largest companies in the US.
“It’s a concentration of data that you just can’t get elsewhere else,” Sileo told Skift, with credit card numbers and other personal information left vulnerable.